Configure a Simple Social Login with Facebook on Your CDK Environment
Author: |
Shankar Raman |
Created at: |
Jul 2021 |
Updated at: |
May 2022 |
Introduction
ForgeRock Identity Platform supports authentication through social identity providers such as Facebook and Google, and lets users login to AM using their social provider credentials.
In this article, we configure Facebook as the social identity provider in a CDK deployment.
Note: ForgeRock does not guarantee the individual success developers may have in implementing the code on their development platforms.
Set up a Facebook application
-
Log in to developers.facebook.com with your Facebook credentials.
-
Create an application with these parameters:
-
In the Select an app type screen, select Business:

-
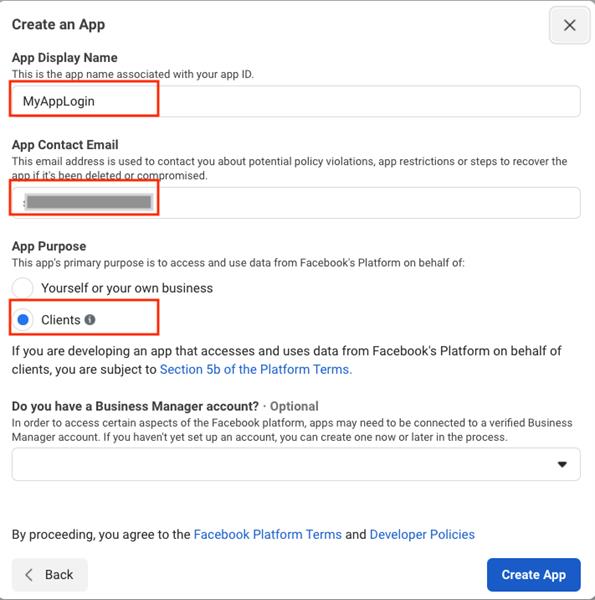
In the Create an App screen, specify suitable values for App Display Name and App Contact Email. Select Clients as the App Purpose:
-
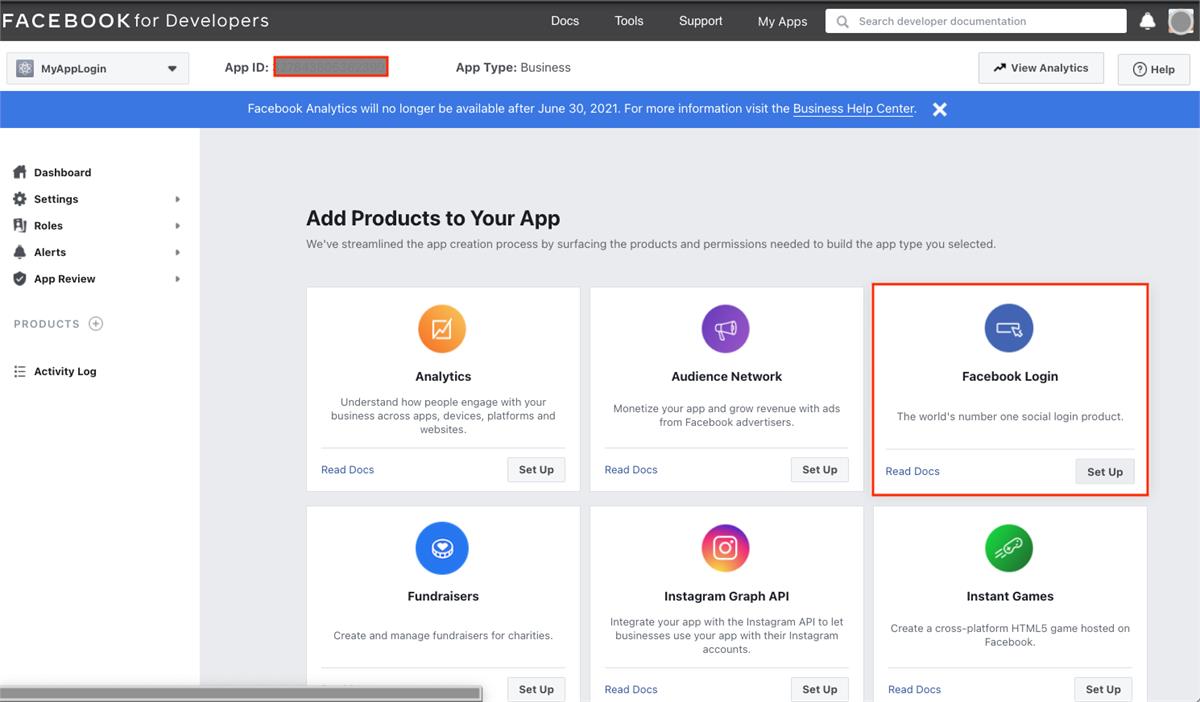
In the Add Products to Your App screen, select Facebook Login:
-
Select Web as the platform for this app:

-
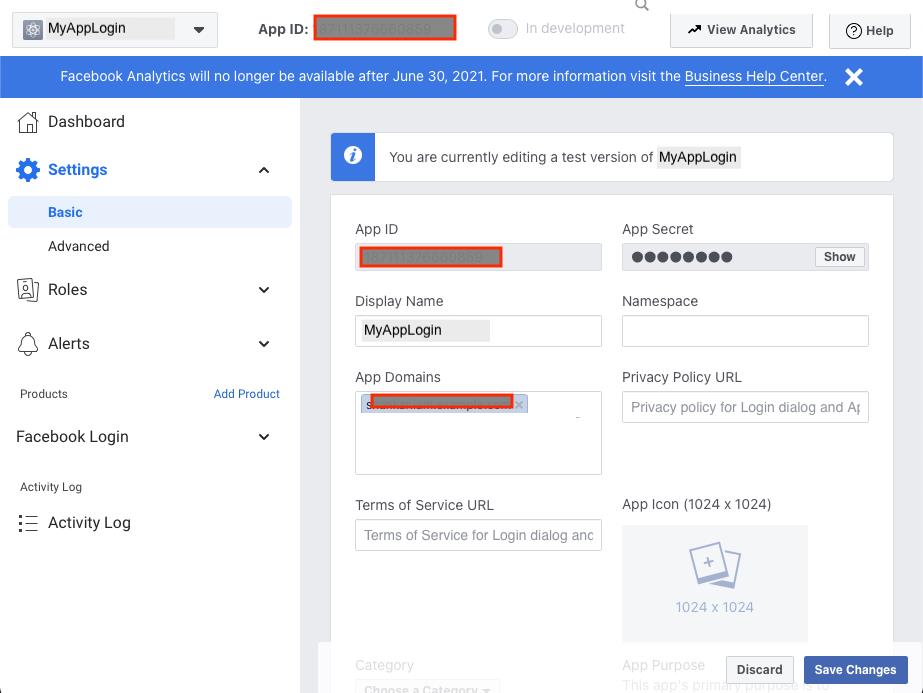
In your application page, navigate to Settings > Basic. Then, click Show in App Secret. Note the App ID and App Secret values. You will need these to configure the social identity provider in AM.
-
In the Basic settings page, specify the application domain, such as iam.example.com, for your AM deployment in App Domains:
-
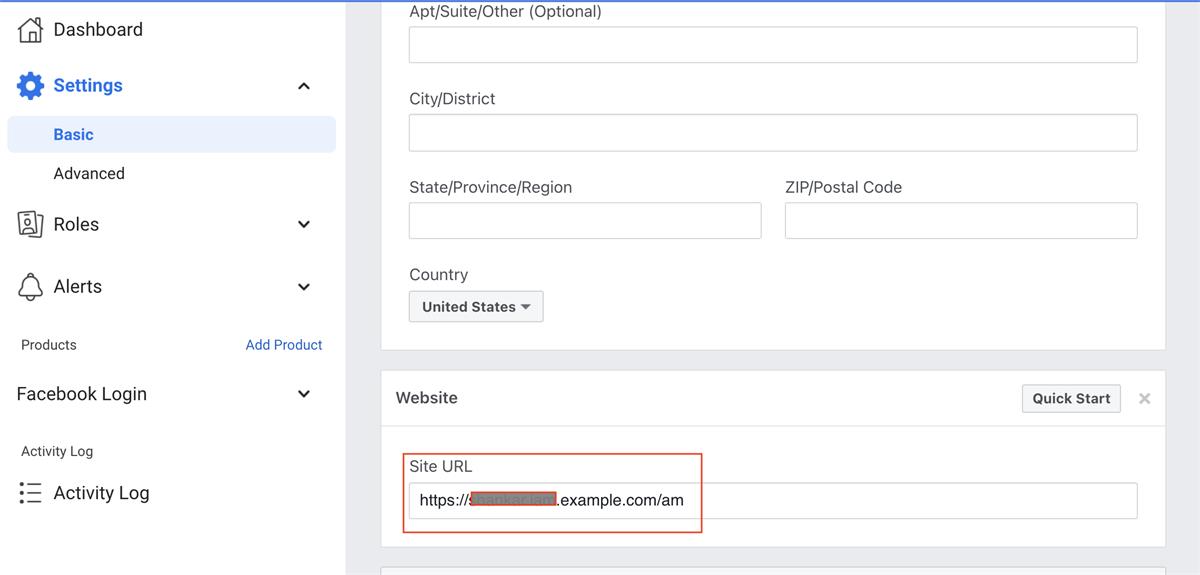
Scroll down and add the URL for your AM deployment in the Website Site URL:
-
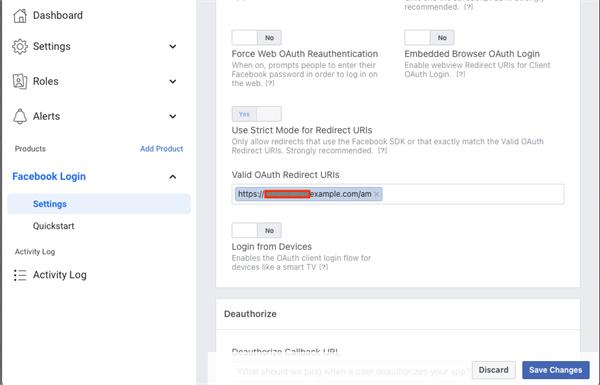
Go to Facebook Login > Settings and specify the URL for your AM in the Valid OAuth Redirect URIs:
Configure a social identity provider in AM
-
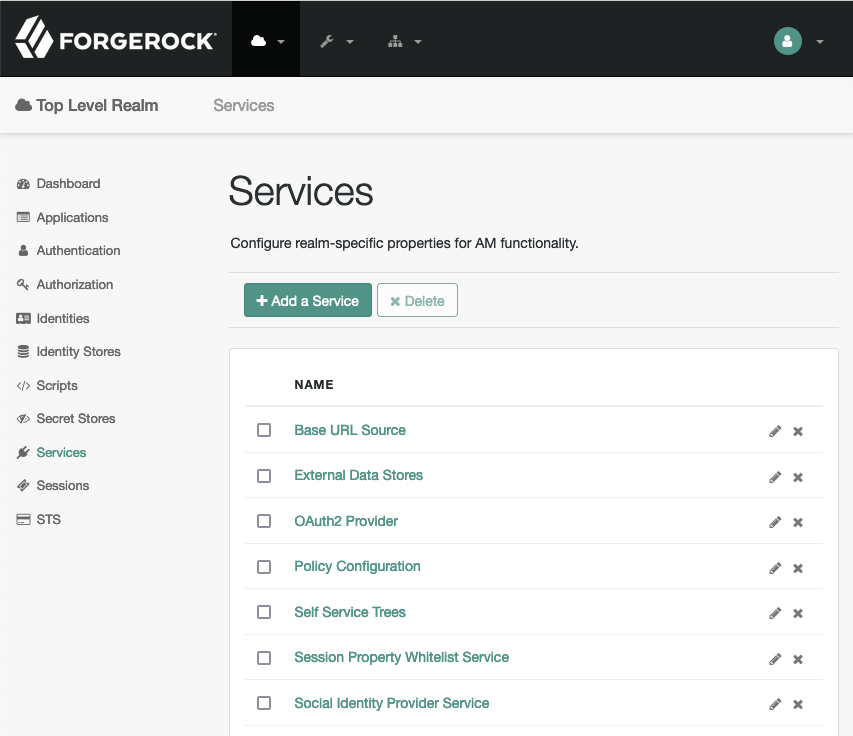
Log in to the AM admin UI in your environment, and navigate to Realms > your realm > Services. Check if Social Identity Provider Service appears in the list of services configured for the realm:
-
If it does not appear in the list, add it: Click Add a Service, and select Social Identity Provider Service from the drop-down list. The service’s configuration page appears.
-
Ensure that the Social Identity Provider Service is enabled:

-
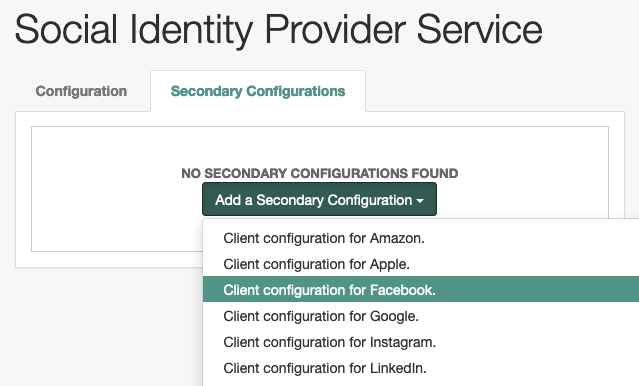
Go to the Secondary Configurations tab. In the Add a Secondary Configuration drop-down list, select Client configuration for Facebook:
-
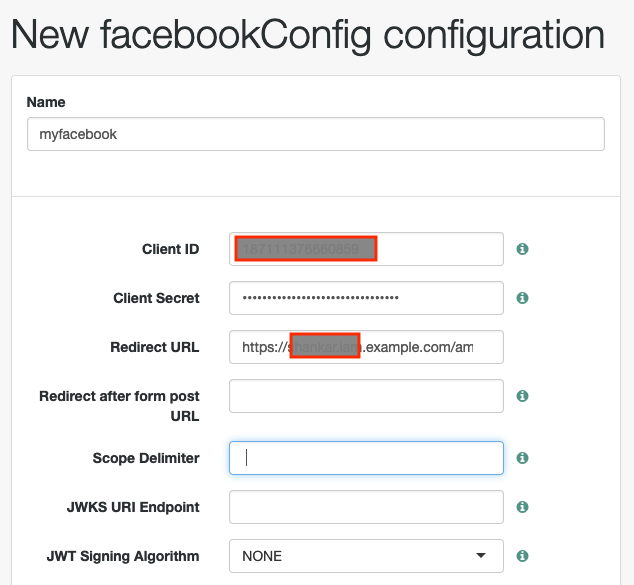
In the New facebookConfig configuration dialog box, enter a Name (in this example, “myfacebook”), your Facebook App ID as the Client ID, and “App Secret” as the Client Secret. Enter your AM URL as the Redirect URL, and a space character " " as the Scope Delimiter. Save your configuration:
-
Notice that some of the parameters are automatically generated for you:

Configure an authentication tree
To effectively use the social login, you should create/modify an authentication tree which contains two significant nodes:
-
The Select Identity Provider node, which prompts the user to select a social identity provider to register or log in with, or (optionally), continue on with a local registration or login flow. When a provider is selected, the flow continues on to the Social Provider Handler node.
-
The Social Provider handler communicates with the selected provider, and then collects the information provided after the user has authorized the service. It then takes that information and runs a transformation script to prepare it.ForgeRock Identity Platform includes a transformation script called Normalized Profile to Managed User, which this node uses to transform the identity object gathered from the identity provider into a ForgeRock Identity Platform object.The node then queries IDM to see if the user already exists. If the user exists, they are logged in. If the user does not exist, create them.
To create a basic social authentication tree:
-
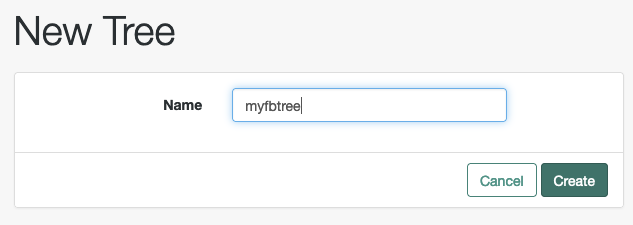
In the AM admin UI, go to Realms > Realm Name > Authentication > Trees, and create a new tree:
-
Decide whether users can log in with their AM credentials, and add the relevant nodes to the tree. Social authentication trees allowing local authentication might look like the following:

-
Configure the Social Provider Handler Node:
-
In theTransformation Script field, configure Normalized Profile to Identity. This script will transform the normalized identity provider’s profile object into the appropriate user profile attributes of the realm’s identity store.
-
In the Client Type field, select BROWSER.
-
Verify you can log in to AM using Facebook
To verify that you can log in using Facebook:
-
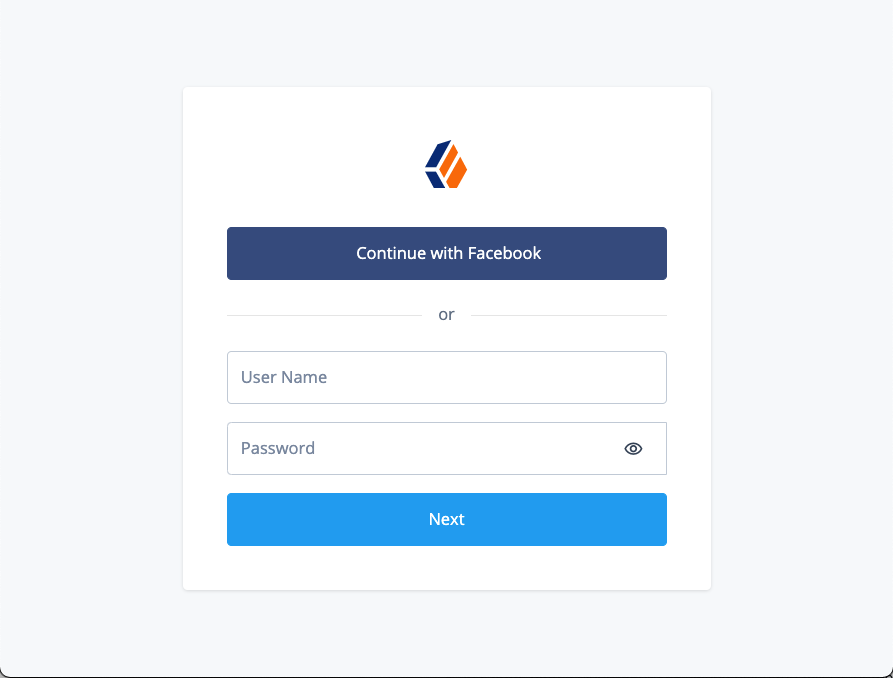
Access the social login tree you created in a new web browser window, for example: https://my-namespace.iam.example.com/am/?service=myfbtree. Notice that you get an option to Continue with Facebook. Click Continue with Facebook:
-
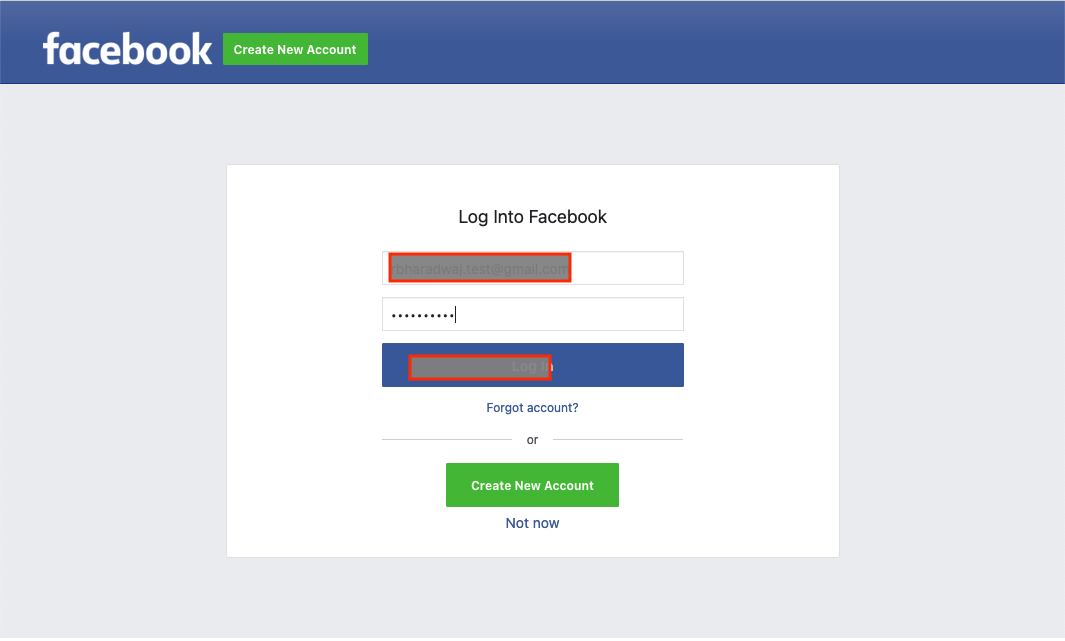
Log in using your Facebook credentials:
-
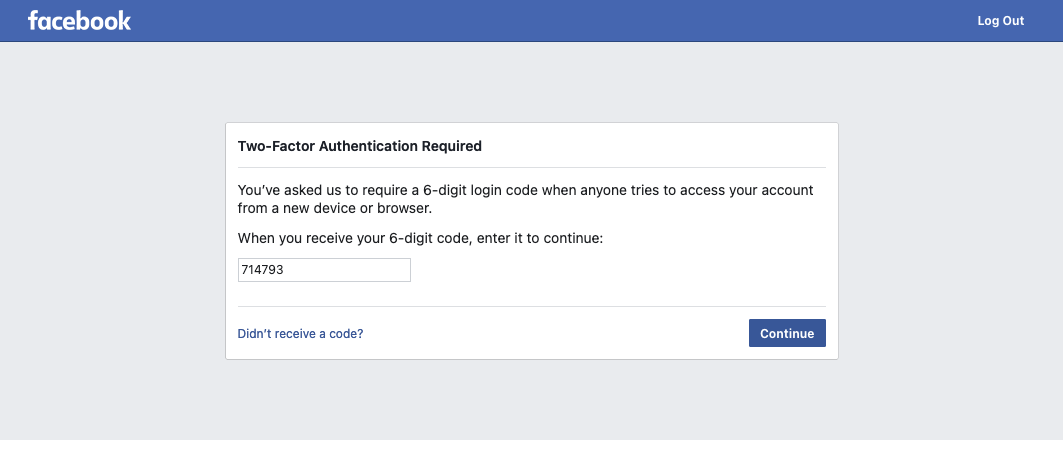
If a Facebook TFA dialog box appears, provide the necessary code:
-
Notice that you are successfully logged in to the user’s profile page on your CDK:

There you have it, a simple way to configure Facebook as social identity provider in your CDK deployment.
More from this author:
Introduction Self-service operations, such as resetting one’s own password, getting forgotten usernames, and others, require access to email. Mailhog is a lightweight utility for sending and viewing email messages in a Kubernetes cluster, especially for development and test purposes. Note: Mailhog is not meant for use in production environments. ForgeRock does not guarantee the individual success developers may have in implementing the code on their development platforms. References Mailhog …