ForgeRock Identity Cloud: Validating a known user’s identity
Author: |
Lucy Billington |
Created at: |
Jun 2023 |
Updated at: |
Jul 2024 |
Overview
Validating a known user’s identity is the process of verifying the identity of someone who is already known in a particular system or service. This process ensures that the user accessing the system is the person they claim to be. The methods used for validation can vary depending on the context and the level of security required.
ForgeRock Identity Cloud offers several capabilities for validating a known user’s identity. These include:
Journey orchestration
What is it?
With journey orchestration, you can define the steps a user will take to complete an identity event such as authentication, registration or password reset. These steps can branch based on user actions (such as a failed authentication attempt), or contextual information gathered as part of the event (such as the device location).
How is it achieved in Identity Cloud?
ForgeRock’s Intelligent Access Journeys provide a no-code / low-code drag-and-drop interface for creating flexible, context-driven user journeys.
Identity Cloud comes with an extensive library of out-of-the-box nodes to build user journeys for multiple use cases. To get you started, Journey templates are provided for login, registration and user self-service. An example of a simple login journey is shown here:
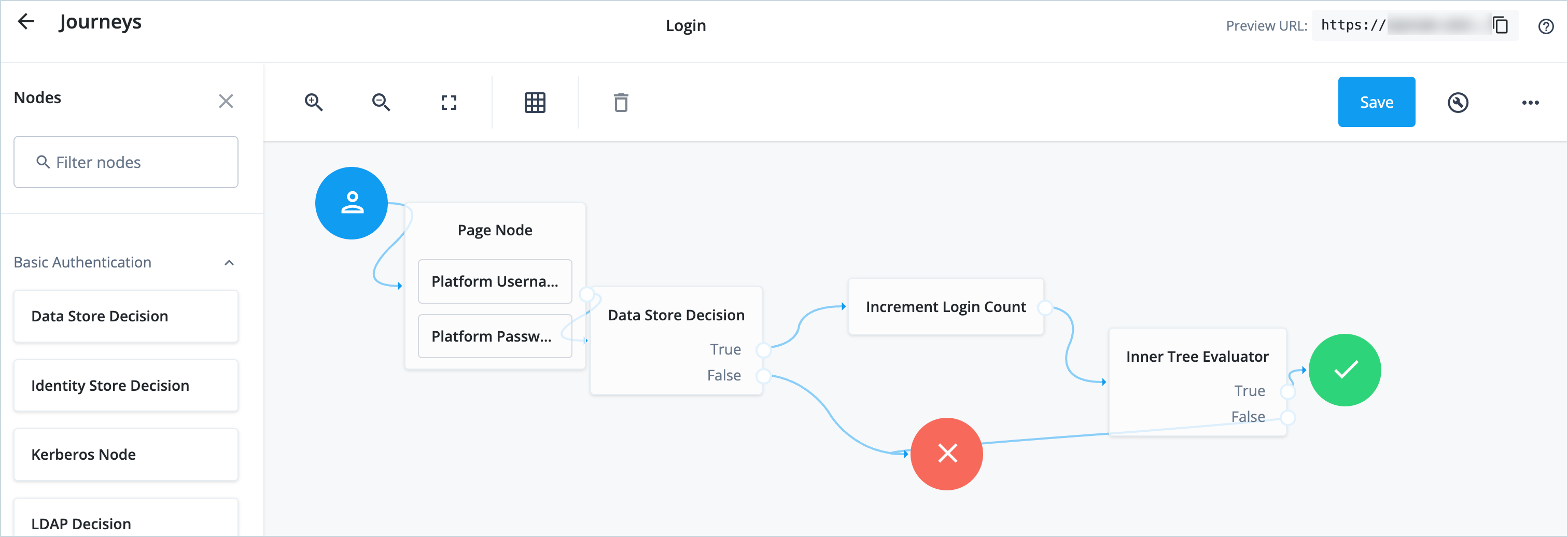
Journeys can be constructed to meet your organization’s needs. By evaluating the context, for example, the user’s device location, a journey can automatically challenge for stronger authentication techniques such as multi-factor authentication (MFA) in higher-risk scenarios, while offering easier paths for lower-risk scenarios.
For further information on achieving journey orchestration with Identity Cloud, see:
Business benefits
Intelligent Access Journeys provide a framework for creating authentication journeys without the need for coding for most use cases. Instead of designing user journeys individually for each application, organizations can design journeys once and apply them globally. This approach eliminates the need for weeks of coding, testing, and re-coding multiple integrations.
By utilizing a wide array of pre-built journey nodes and pre-integrated partner solutions, organizations can design user journeys in a single session, resulting in significant savings in IT and development costs.
Further information on the many business benefits of ForgeRock’s Intelligent Access Journeys can be found in our Intelligent Access white paper.
Multi-factor authentication
What is it?
With multi-factor authentication (MFA), identities are verified through two or more categories of authentication. A common definition of authentication categories is something you know (such as a password), something you have (such as a one-time passcode), and something you are (such as a biometric). This provides a more secure method for users to access their accounts.
Since data breaches and fraud have escalated in recent years, the need for multi-factor authentication has become critical to reducing risk. In authentication flows, MFA may be requested for every authentication or only when there is an elevated risk.
How is it achieved in Identity Cloud?
To achieve MFA in ForgeRock Identity Cloud you can simply configure Intelligent Access Journeys with at least one authentication node from two or more authentication categories.
ForgeRock ships with a range of MFA options including:
-
Open Authentication (OATH) to enable one-time password (OTP) authentication.
-
Push authentication to receive push notifications on a device as part of the authentication process.
-
Web Authentication (WebAuthn) to authenticate by using an authenticator device such as a fingerprint scanner on a laptop or phone.
For example, this user journey shows how you can construct a simple one-time password authentication flow using OATH nodes:
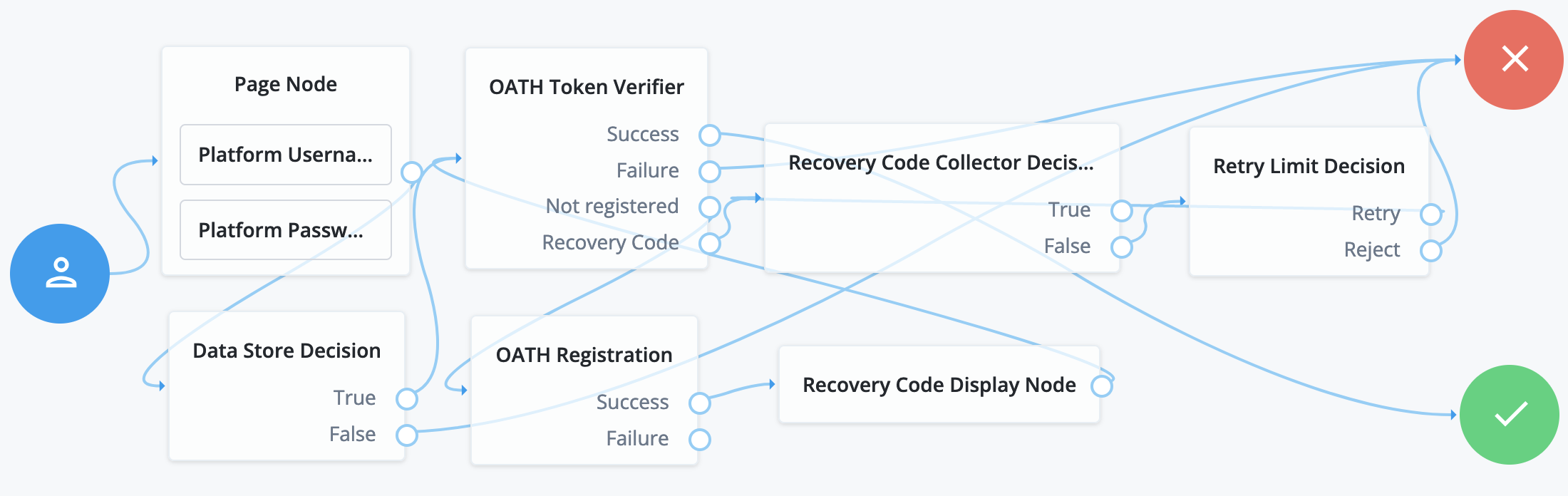
The journey can be easily extended to include out-of-the-box nodes to enable the user to obtain an authenticator app, register an MFA device or skip the registration process, or opt out of MFA.
For more advanced authentication capabilities, you can extend journeys with ForgeRock Marketplace nodes by integrating third-party services into your user journeys. These may include nodes for identity proofing, fraud protection, behavioral biometrics, and more.
For further information on achieving MFA with Identity Cloud, see:
-
Does the ForgeRock solution offer multi-factor authentication (MFA)?
-
Use case: Configure OATH-based token two-factor authentication in ForgeRock Identity Cloud
-
Multi-Factor Authentication (training video)
-
Experience dynamic MFA (ForgeRock Experience Center demo)
Business benefits
By adding an extra layer of security to protect applications and services, MFA significantly reduces the risk of unauthorized access, phishing attacks and password breaches. Additional factors, such as one-time passcodes and biometric checks, make it significantly more difficult for attackers to impersonate legitimate users.
MFA helps organizations comply with specific data protection regulations that require the implementation of strong authentication mechanisms. For example, the Payment Card Industry Data Security Standard (PCI DSS), General Data Protection Regulation (GDPR), or Health Insurance Portability and Accountability Act (HIPAA).
For organizations that handle customer data, implementing MFA can also enhance trust by demonstrating a commitment to protecting sensitive information, fostering customer loyalty, and improving the organization’s reputation.
Contextual authentication
What is it?
With contextual authentication, a user’s identity is verified using various contextual factors such as location, device information or user behavior.
By considering contextual factors, authentication systems can evaluate the risk associated with each authentication attempt. Depending on the level of risk, additional security measures may be triggered, such as requesting additional verification steps, sending one-time passcodes, or flagging the activity for further review.
How is it achieved in Identity Cloud?
Contextual authentication is achieved through Intelligent Access Journeys and, in some cases, associated client-side scripting or SDKs, and authorization policies.
With Intelligent Access Journeys, signals such as context (for example, IP address, operating system, browser, device, time of day), behavior (for example, ‘does the user log in at a particular hour’, or ‘is the location familiar’), and risk-based factors (such as ‘is the user accessing sensitive data’), can be considered. If an environmental or context attribute changes (for example, the user’s IP address), reauthentication or a stronger credential can be requested.
You can apply contextual factors at the time of authentication as well as at any point during a digital session. This continuous security approach ensures the authenticity of identities at all times and can mitigate risk whenever an anomaly is detected.
Identity Cloud also offers an Autonomous Access service, which uses the power of artificial intelligence (AI) and machine learning (ML) to monitor login requests in real time. By assigning a risk score to every login attempt based on a variety of factors and using that score to instantly apply the appropriate level of friction based on risk, Autonomous Access can block malicious attempts and add authentication steps when it detects anomalous behaviors.
For further information on achieving contextual authentication with Identity Cloud, see:
Business benefits
By analyzing multiple factors and patterns, contextual authentication helps organizations identify potential security threats and reduces the risk of unauthorized access to services and applications.
Using Intelligent Access Journeys and a variety of authorization policy enforcement options, organizations can make continuous security decisions and support Zero Trust and Gartner’s Continuous Adaptive Risk & Trust Assessment (CARTA).
For organizations that handle customer data, implementing contextual authentication can enhance trust and confidence by demonstrating a commitment to protecting their sensitive information, fostering customer loyalty, and improving the organization’s reputation.
Passwordless authentication
What is it?
With passwordless authentication, a user’s identity is verified without the need for traditional passwords. Common approaches to passwordless authentication include biometric authentication, one-time passcode (OTP), and Web Authentication (WebAuthn) based on FIDO2 standards and passkeys (also known as multi-device credentials).
According to Gartner, by 2025 more than 50% of the workforce and more than 20% of customer authentication transactions will be passwordless, up from less than 10% today.
How is it achieved in Identity Cloud?
Web Authentication (WebAuthn)
With the increased adoption of FIDO2 and WebAuthn, strong authenticators such as Windows Hello and Apple’s Touch ID are now built into many devices. ForgeRock Identity Cloud includes a set of passwordless authentication features designed to support the WebAuthn standard.
Identity Cloud comes with authentication nodes that make it easy to build passwordless user journeys for your WebAuthn use cases. You can simply drag and drop the pre-built WebAuthn nodes and adjust the authentication journey to meet your needs, similar to this example:
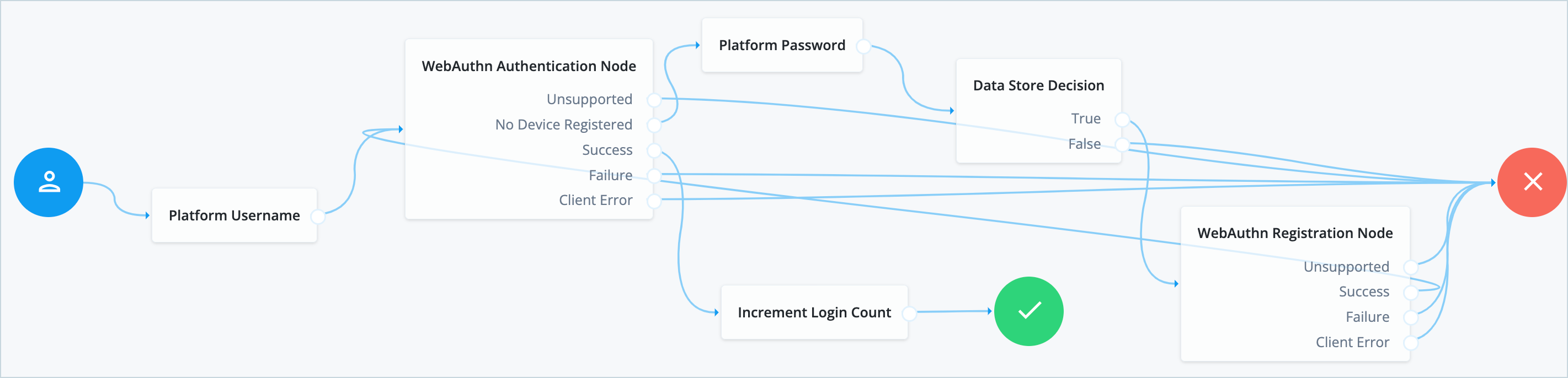
For further information on achieving passwordless authentication with FIDO2 and WebAuthn in Identity Cloud, see:
-
Use case: Configure passwordless login in ForgeRock Identity Cloud
-
Go Passwordless (whitepaper)
-
Fully Eliminate Passwords - workforce (white paper)
-
Go Passwordless (experience center demo)
Enterprise Connect Passwordless
For workforce use cases, ForgeRock offers a passwordless authentication solution called Enterprise Connect Passwordless. This replaces the standard username and password login mechanisms for Windows and Apple desktops, allowing organizations to utilize MFA for login, and apply additional authentication policies for desktop access.
Enterprise Connect Passwordless provides a comprehensive solution for passwordless authentication, including various authentication methods, no-code orchestration journeys, and seamless application integration.
For further information on achieving passwordless authentication with Enterprise Connect Passwordless, see:
Business benefits
Passwordless authentication can enhance security by eliminating the risk of weak or stolen passwords, reduce the burden of password management for users, and simplify the authentication process.
CIAM: Passwordless authentication offers a better experience to customers by eliminating cumbersome logins. It also enables organizations to also strengthen their defenses against password-based attacks, such as phishing and malware.
Workforce: Passwordless authentication provides friction-free access to business resources to increase workforce productivity and operational efficiencies. With Enterprise Connect Passwordless, organizations can move from traditional usernames and passwords to processes that introduce passwordless at their own pace.