Use case: Configure passwordless login in ForgeRock Identity Cloud
Author: |
Lucy Billington |
Created at: |
Dec 2022 |
Updated at: |
Dec 2022 |
Use case overview
Enabling your organization to design secure and seamless login journeys without the need for passwords is a common use case that is easily implemented in ForgeRock Identity Cloud.
Passwordless authentication not only improves the user experience by avoiding the need to remember multiple passwords but it also reduces an organization’s attack surface by virtually eliminating credential theft arising from phishing attacks, password reuse, credential stuffing, keyloggers, and more.
With the increased adoption of FIDO2 and Web Authentication (WebAuthn), strong authenticators such as Windows Hello and Apple’s Touch ID are now built into many devices. With Identity Cloud, you can easily design simple user journeys that enable passwordless login with FIDO2-enabled devices.
Steps to achieve this use case
This example use case demonstrates how to create a simple WebAuthn login journey. With WebAuthn, end users can authenticate by using a FIDO2-enabled device such as the fingerprint scanner on their laptop or phone.
To create a simple WebAuthn login journey:
-
Sign in to the Identity Cloud admin UI using your admin tenant URL, in the format
https://<tenant-name>/am/XUI/?realm=/#/. -
Go to Journeys > New Journey.
-
Enter a unique name for the WebAuthn journey, select which identities will authenticate using this journey, (optionally) enter a journey description, and click Save.
-
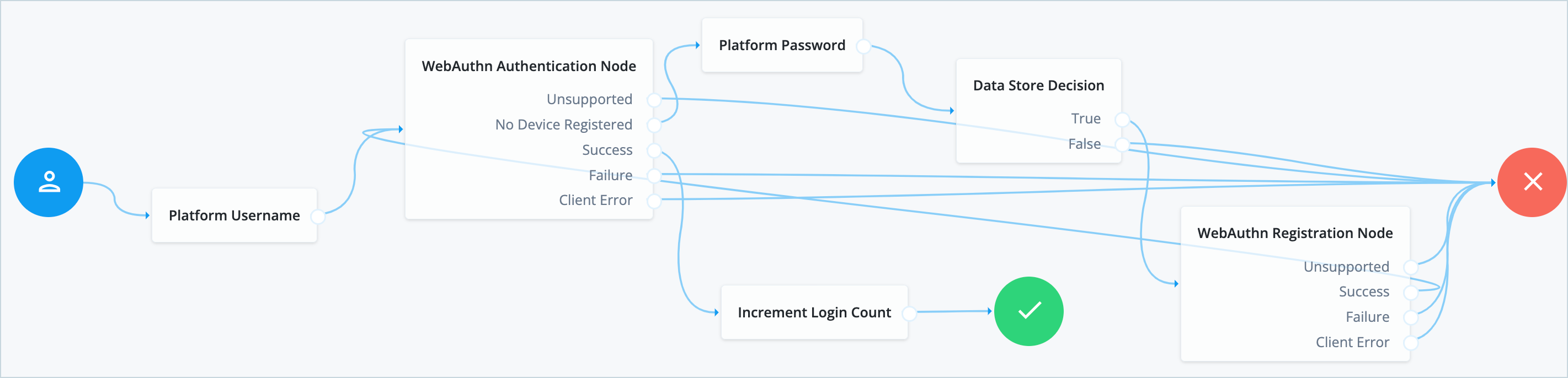
Create a journey similar to this, keeping the default node configurations as they are:
-
Click Save to save the journey.
Node descriptions:
-
Platform Username - Prompts the user to enter their username. See Platform Username node for further information.
-
WebAuthn Authentication Node - Checks whether the device supports WebAuthn and allows users to use a registered FIDO2 device during authentication. See WebAuthn Authentication node for further information.
-
Platform Password - Collects the user’s password if no FIDO2 device has been registered. See Platform Password node for more information.
-
Data Store Decision - Verifies that the username and password values match those in the data store configured for the realm. See Data Store Decision node for further information.
-
Increment Login Count - Increments the successful login count property of a managed object. See Increment Login Count node for further information.
-
WebAuthn Registration Node - Allows users of supported clients to register FIDO2 devices for use during authentication. See WebAuthn Registration node for further information.
In this journey, if the device registration succeeds, the user is returned to the WebAuthn authentication step. This feedback loop isn’t strictly necessary but is common in passwordless authentication.
NOTE: This is an example of a simple WebAuthn journey. Other nodes you may wish to include in your WebAuthn journey for more complexity include WebAuthn Device Storage node, Recovery Code Collector Decision node, and Recovery Code Display node.
Testing the use case
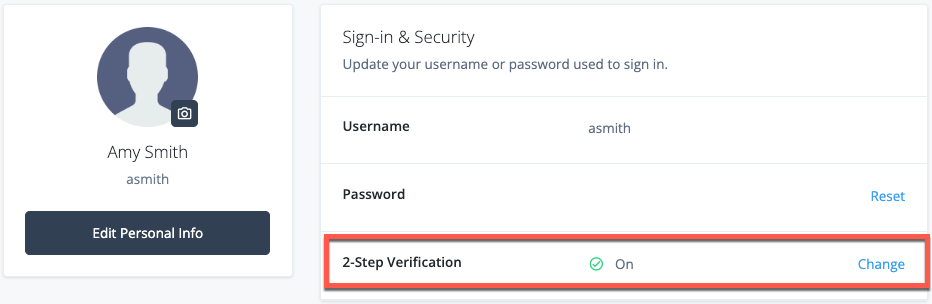
To test the use case, make sure that your test end user doesn’t have any devices already registered on their profile.
NOTE: The test should be run on a client that supports WebAuthn. See MFA: Web authentication (WebAuthn) for further information. The steps may differ slightly depending on your browser type; in this example, we’re using Google Chrome.
Register a new FIDO2 device
-
In the Identity Cloud admin UI, go to Journeys.
-
Click the WebAuthn journey you created previously and copy the Preview URL.
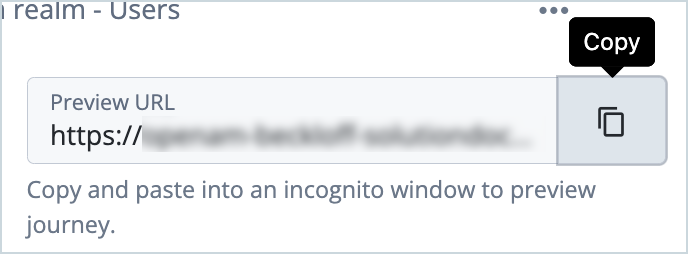
-
Paste the preview URL into a browser using Incognito or Browsing mode.
-
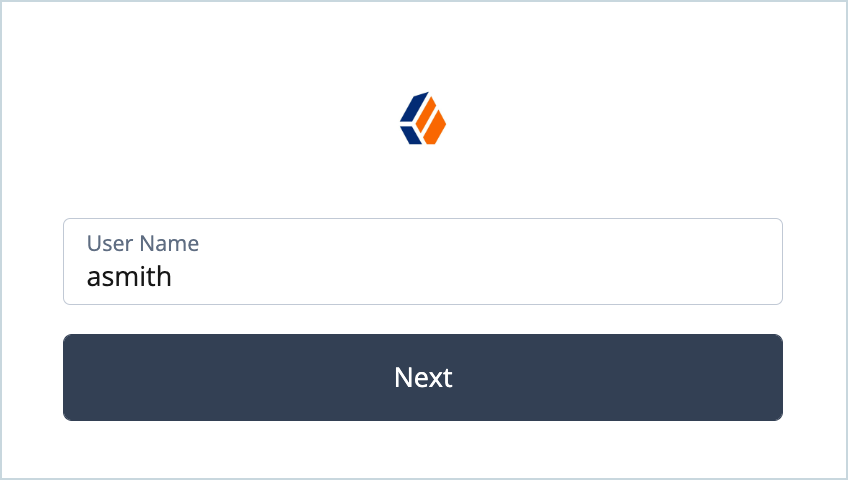
Enter the test user’s username in the Sign In screen and click Next.
-
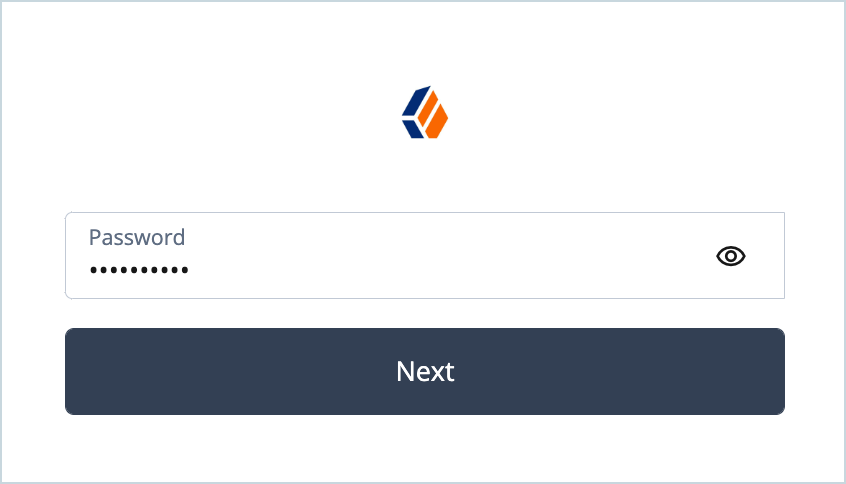
Enter the test user’s password and click Next.
-
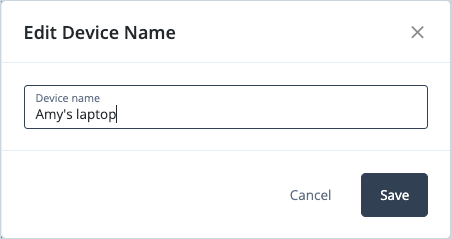
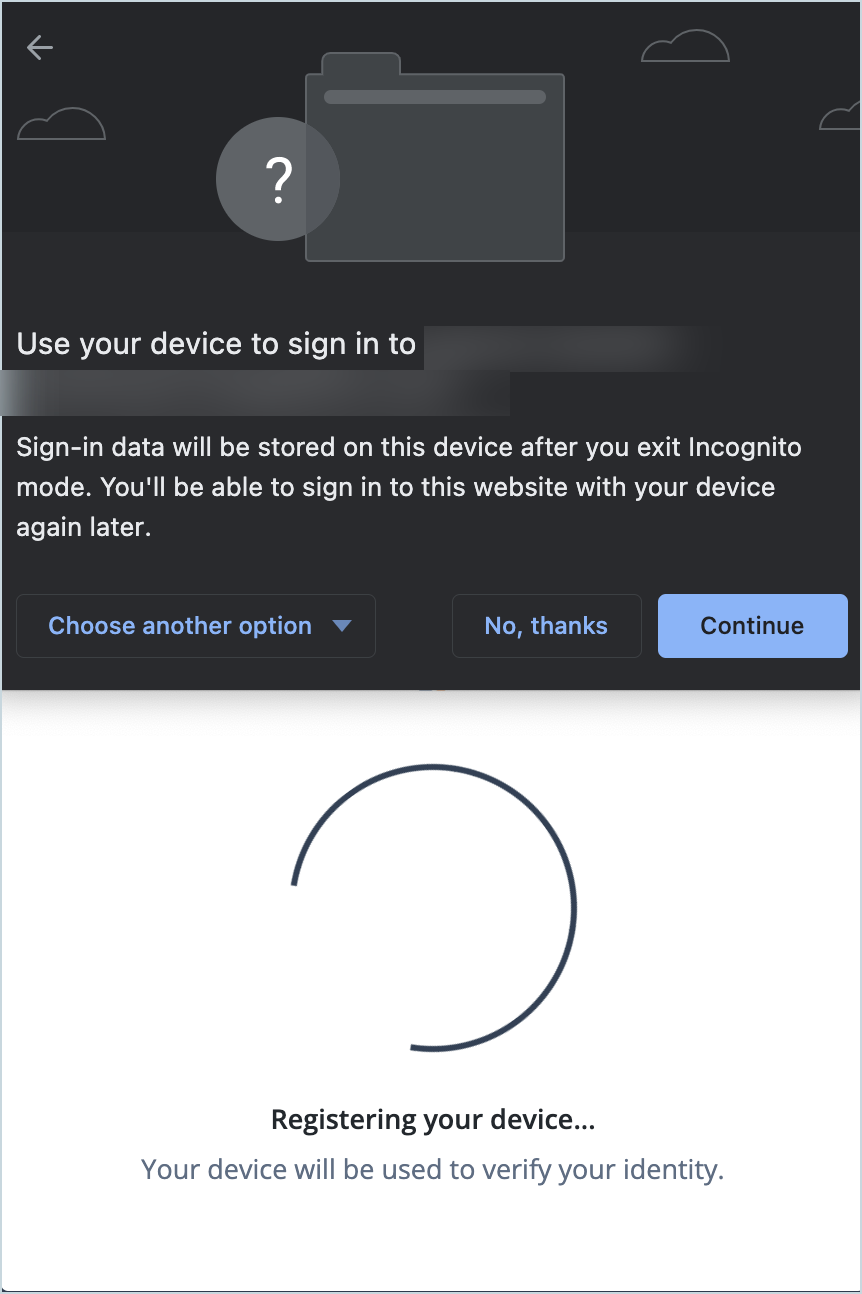
Select the method of registering the device. In this example, we’ll choose
This device.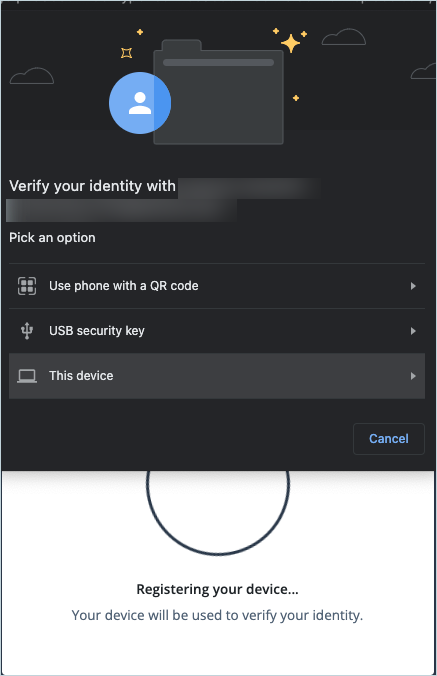
-
Click Continue.
-
Scan your fingerprint when prompted, for example with Touch ID:
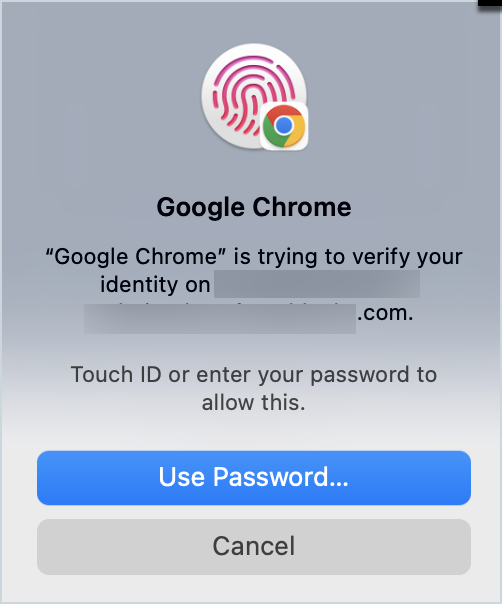
Once your identity has been verified and the device has been associated with the account you are successfully logged in as the test user.
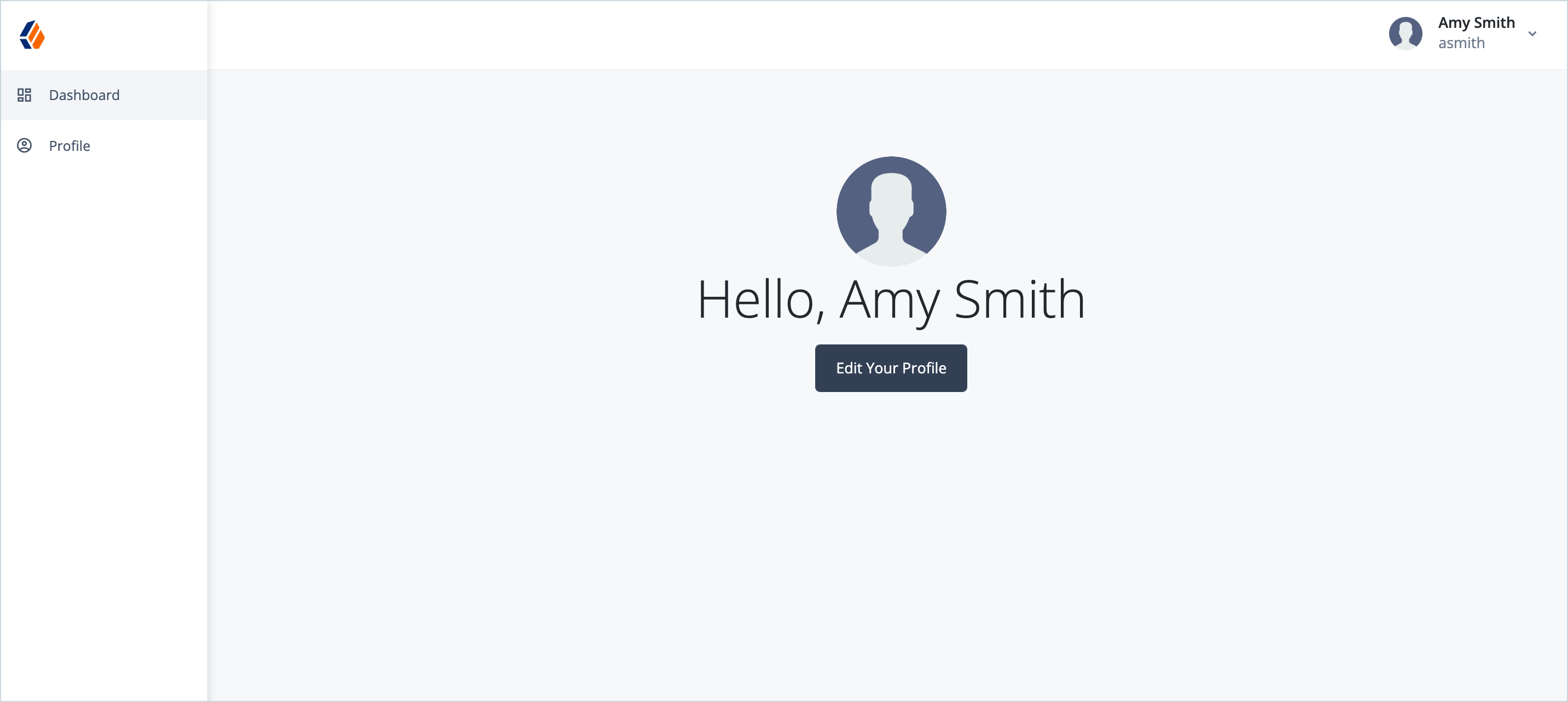
Next time you log in as the test user using the WebAuthn journey you won’t be asked for a password, just a username and fingerprint scan.
Conclusion
This use case has demonstrated how you can easily create passwordless login journeys using out-of-the-box nodes in Identity Cloud.