Moving to ForgeRock Identity Cloud
Author: |
Mark Nienaber |
Created at: |
Oct 2021 |
Updated at: |
Feb 2023 |
You’ve decided to move to ForgeRock Identity Cloud! First of all, congratulations! We look forward to helping you simplify your life, lower your risks, realize business benefits earlier, and provide you with the latest technology wrapped up in our ForgeRock Identity Cloud Platform.
Let’s answer some of the more common questions:
How will you build your ForgeRock Identity Cloud solution?
During your ForgeRock Identity Cloud project, ForgeRock gives you access to our Identity Cloud Technical Consultants, and a Customer Deployment Manager who will work with your organization and your chosen Partner/SI to build your initial offering. This will involve assistance in designing and building your Identities and applications to meet your organization’s requirements, migrating your users to the platform, connecting your required applications, and whatever other requirements you have.
Customers can create support tickets at any time through Backstage. These tickets can be used for moving configuration between environments and secrets management. Learn about promoting configuration.
Where is ForgeRock Identity Cloud?
ForgeRock is a proud Google Cloud Premier Partner. As such, our Identity Cloud solution resides in the regional Google Cloud Platform (GCP). Engineered for Google Cloud, ForgeRock Identity Cloud is built with a multi-tenant cloud architecture with full customer isolation. More information about ForgeRock’s partnership with Google Cloud can be found [here](https://www.forgerock.com/partner/google-cloud).
What is available in ForgeRock Identity Cloud?
Access to Identity Cloud is done through a variety of packages, each giving you access to more and more underlying functionality.
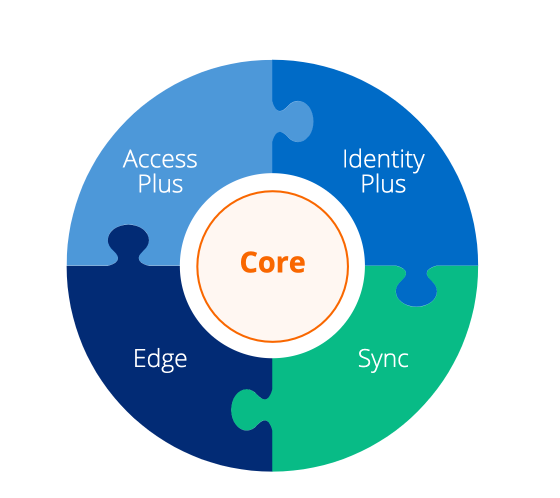
For detailed information about these packages, go here. Underlying the ForgeRock Identity Cloud solution is our comprehensive ForgeRock Identity Platform.
What components sit in ForgeRock Identity Cloud?
At a very high level, ForgeRock Identity Cloud contains the following.
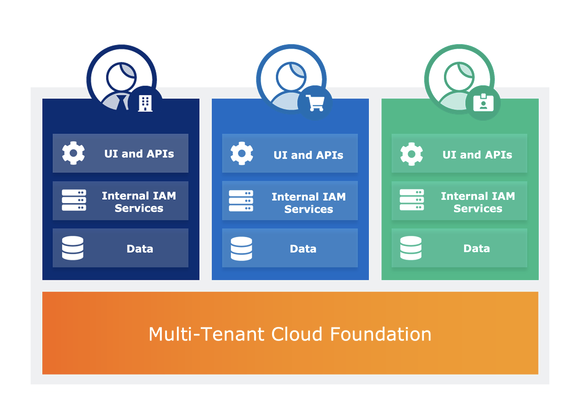
ForgeRock is responsible for managing these components, including upgrading, monitoring, promoting configuration, and all other maintenance tasks. What this means for you is:
* No deployments * No upgrades * No system management * Round the clock monitoring
Also, during the deployment, our project team can help you design and build the functionality inside your ForgeRock Identity Cloud.
What components sit outside of ForgeRock Identity Cloud?
Some of the components will sit outside of Identity Cloud, but are still part of your overall solution. These can reside in your own cloud, or on-premise; the actual location will depend on your use cases and organization’s structure. These components are the responsibility of the organization to install and maintain. This will require the provisioning of resources like hardware/virtual machines/containers, and your chosen SI. Our Technical Consultants can help you ensure your solution is designed with high availability, performance, and security in mind.
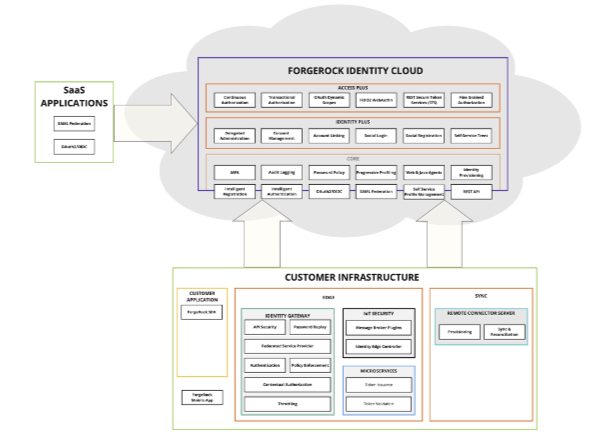
ForgeRock Identity Gateway (IG) can play many roles, and is often called the Swiss Army knife of the ForgeRock Identity Platform. For more information about IG and its use cases, see here.
A common example is an SSO-enabled reverse proxy protecting applications. IG can enforce SSO by Identity Cloud, and also ensure the user is authorized to access the resources. In this simple example, your authentication journeys and authorization policies are configured in Identity Cloud, and IG ensures applications are protected correctly to meet organizational objectives. While there are many other use cases for IG, the point is that IG sits outside of Identity Cloud, but securely communicates to offer protection.
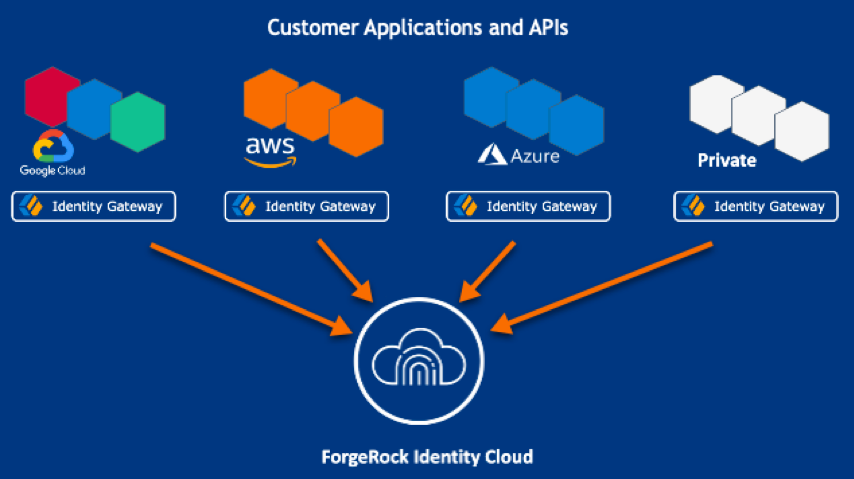
The diagram below, which can be found in more detail
here,
illustrates how IG protects applications and APIs backed by Identity
Cloud.
ForgeRock’s Policy Agents also sit to offer SSO/Web protection, often installed on the applications server. The actual use cases will dictate the correct component. More information on Policy Agents can be found here.
Remote connector server
Data synchronization to/from ForgeRock Identity Cloud to your on-premise applications, i.e., Active Directory, ForgeRock Directory Services, and/or other supported applications, is a very common requirement. You’ll find documentation regarding the remote connector server (RCS) setup on the Identity Cloud Connect Identities page.
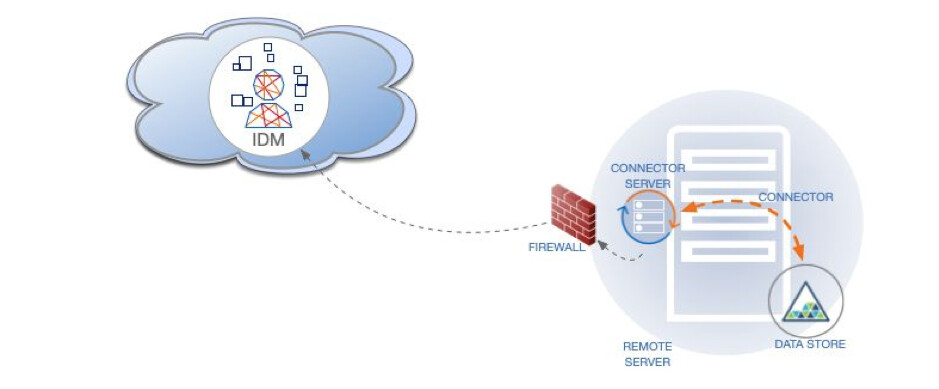
In order to securely connect from ForgeRock Identity Cloud into your organization, ForgeRock provides the remote connector server (RCS). The RCS is a Java application that is installed inside the organization’s boundary, and contains the connectors that are required to communicate to various supported applications. The IDM component of ForgeRock Identity Cloud has a built-in connector server, and when IDM is installed inside the organization, can use its built-in server. Because ForgeRock Identity Cloud is now out there in the cloud, it is necessary to separate IDM and its connector server to ensure that traffic to/from cloud to on-premise is secure.
The following diagram illustrates a typical RCS architecture where the RCS is placed behind the firewall. This diagram and more information can be found in the IDM documentation.
Software Development Kits
ForgeRock’s services are available over our common REST API, including authentication, authorization, management of identities, and even the service itself. To make these REST services even easier to consume, ForgeRock provides you with our software development kits (SDKs), supported on iOS and Android, as well as JavaScript. The SDKs eliminate unnecessary complexity and increase platform agility. The SDKs can be embedded into your web page or app to add capabilities like SSO, device profiling, and user registration, all backed by Identity Cloud. ForgeRock provides tutorials and examples of SDK’s usage that the organization’s UI team can use when developing their ForgeRock Identity Cloud-secured applications. FogeRock provides comprehensive documentation on our SDK’s here and an entire site dedicated to the SDK here.
SIEM Tools and Auditing
ForgeRock Identity Cloud provides an API to retrieve and view the logs, and stores the logs for 30 days. More details about Identity Cloud audit logging can be found here. Each of our customers use their own SIEM tools to collate and present audit data according to internal policies and procedures. The setup of the SIEM tools like Splunk and QRadar are therefore the responsibility of the organization.
ForgeRock Community
These repositories are provided by the community of ForgeRock users. They are in no way supported or tested by ForgeRock. - ForgeRock Community
Other Articles by This Author
![]() Moving to ForgeRock Identity
Cloud
[.badge-category__name#Architecture#]
Moving to ForgeRock Identity
Cloud
[.badge-category__name#Architecture#]
You’ve decided to move to ForgeRock Identity Cloud! First of all, congratulations! We look forward to helping you simplify your life, lower your risks, realize business benefits earlier, and provide you with the latest technology wrapped up in our ForgeRock Identity Cloud Platform. Let’s answer some of the more common questions: How will you build your ForgeRock Identity Cloud solution? Where is ForgeRock Identity Cloud? What is available in ForgeRock Identity Cloud? What components sit in Fo…
Originally posted on marknienaber.medium.com Protecting an application with ForgeRock Identity Gateway Using Identity Gateway to send HTTP Headers to a protected backend application Introduction ForgeRock Identity Gateway integrates web applications, APIs, and microservices with the ForgeRock Identity Platform. For more information about IG, see About IG. We will solve a relatively common use case in this blog. We are protecting an application using IG, the requirements are: The application…
By Mark Nienaber Originally posted on marknienaber.medium.com Summary Configuring ForgeRock Identity Cloud as a SAML identity provider using ForgeRock Identity Gateway as SAML service provider. Introduction This article will guide you through configuring IG as a SAML 2.0 Service Provider (SP), delegating authentication to ForgeRock Identity Cloud, our Identity Provider (IDP). This solution uses SP-Initiated Single Sign On. Specifically, we aim to address two commonly requested ForgeRock…
This article comes from an issue raised by multiple customers, where ForgeRock Access Management (AM) was not able to retrieve a user’s group memberships when using Active Directory (AD) as a datastore with nested groups. I’ve read in different docs about the “embedded groups” expression, as well as the “transitive groups” or “recursive groups” or “indirect groups”, and finally, the “parent groups” expressions. I’m just quoting them all here for search engines. As a consequence, it was not, for…