Use case overview
Users often prefer to authenticate using their social media accounts since it reduces the number of passwords they need to remember and allows them to sign in quickly if they’re already logged in to a social media account.
Identity verification using a social identity provider, such as Google or Facebook, is a common use case that is easily implemented in ForgeRock Identity Cloud.
Identity Cloud supports many social integrations out of the box. In this article, we’ll focus on Google as the social identity provider.
Steps to achieve this use case
The use case has two stages:
- Configure Google social integration
- Create a social login journey
Configure Google social integration
For information on configuring Google as a social identity provider in Identity Cloud, see Google SSO integration with Identity Cloud for social authentication/registration.
Create a social login journey
For information on building simple social login journeys, see How do I create end user journeys for social registration and login in Identity Cloud?
For an example of a more complex journey that can be used for existing users and the registration of new users, you can download a sample Social Login journey from the ForgeRock Community GitHub.
Once you have downloaded the journey, you can import it into Identity Cloud.
Note that the journey import also includes an inner journey for progressive profiling, so you’ll be importing two journeys.
Social Login sample journey description
The journey has the following flow:
-
The user is presented with a Sign In (Page Node) that offers the option to sign in or register with a social provider.
The social providers offered will depend on the list of enabled providers in the Select Identity Provider node. In our example, Google is the only enabled provider. The option to include local authentication (username and password) for sign in is also enabled.
If the user chooses to continue with the social provider the browser is redirected to Google, allowing the user to log in to Google.
-
After successful authentication with the Google Social Provider, the journey checks whether the user already exists as an identity linked to the returned social account (Social Provider Handler Node).
-
If the user can be identified as an existing user, the user is asked whether to continue or not (Existing Social Link / Choice Collector node).
-
If the user chooses to continue with Proceed, the login count is incremented (Increment Login Count node), the inner tree to request progressive profile attributes is evaluated (Inner Tree Evaluator node using ProgressiveProfile) and the user is logged in.
-
If no existing identity was found in Step 2, but the returned email address is already used (Identify Existing User node), the user is presented with the option to authenticate with an existing password (Matched on Existing / Choice Collector node).
-
If the user chooses to claim the existing identity, the journey continues with a loop (Platform Password node, Data Store Decision node, and Retry Limit Decision node) that allows the user to provide a password (up to three times) that is checked against the data store. If the password can be validated, the journey continues (Patch Object node). Otherwise, the access is denied.
-
If no already linked identity was found in Step 2 and the returned email address is not already used (False path of the Identify Existing User node), the journey offers the user the option to create a new account (Proceed path of No Match - Create / Choice Collector node).
-
If the social provider does not return all required attributes (checked by the Required Attributes Present node), the user is asked to provide the missing attributes (Attribute Collector node) and the local username.
After collecting these attributes, the identity is created in the Identity Cloud tenant (Create Object node).
-
The user is offered the option to provide a local password for subsequent logins ( Provide Local Credentials? / Choice Collector node).
If the user chooses to do so, they are presented with a Page node that collects the local password (Platform Password node).
The provided local password is stored in the local identity store and the journey continues as described in Step 4.
Node reference
- Page node
- Platform Username node
- Platform Password node
- Select Identity Provider node
- Social Provider Handler node
- Choice Collector node
- Inner Tree Evaluator node
- Identify Existing User node
- Data Store Decision node
- Patch Object node
- Increment Login Count node
- Retry Limit Decision node
- Required Attributes Present node
- Attribute Collector node
- Create Object node
Testing a social registration using the sample journey
This test registers an end user in Identity Cloud using Google authentication and the sample social login journey.
For this test, your test user must have a Google account and must not already exist as an identity in your Identity Cloud tenant.
-
In the Identity Cloud admin UI, go to Journeys.
-
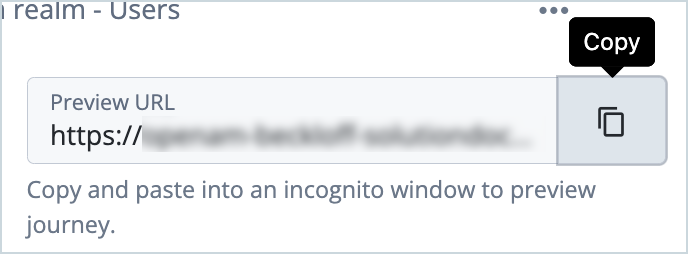
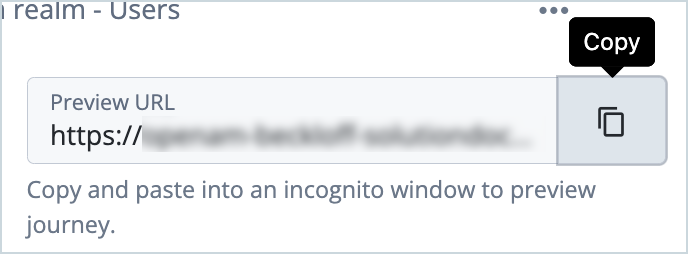
Click the social login journey you created (imported) previously and copy the Preview URL.
-
Paste the preview URL into a browser using Incognito or Browsing mode.
-
In the Sign in screen, click Continue with Google.
-
Sign in to Google using the test user’s credentials.
After successful authentication with the Google Social Provider, the journey checks whether a user with the same email address exists in Identity Cloud.
Since the test user does not already exist in Identity Cloud, you are asked if you want to create a user.
-
Click Next to proceed.
You are asked if you want to create a local password for subsequent logins.
-
Click Next.
-
Enter a local password and click Next.
The registration is now complete and you are logged in and redirected to the default landing page for the end user.
Additional resources
Documentation:
- Social authentication
- How do I create end user journeys for social registration and login in Identity Cloud?
Training videos:
- Identity Cloud Getting Started: Social Registration and Authentication
- Demo: Identity Cloud Getting Started: Social Authentication to Login Journey
Troubleshooting social journeys:
Other social integrations:
- Amazon SSO integration with Identity Cloud for social authentication/registration
- Apple SSO integration with Identity Cloud for social authentication/registration
- Facebook SSO integration with Identity Cloud for social authentication/registration
- LinkedIn SSO integration with Identity Cloud for social authentication/registration
- Microsoft SSO integration with Identity Cloud for social authentication/registration
- Salesforce SSO integration with Identity Cloud for social authentication/registration
- WordPress SSO integration with Identity Cloud for social authentication/registration
- Yahoo SSO integration with Identity Cloud for social authentication/registration
Acknowledgements: Andre Posner