A Scripted Approach for Creating and Using Service Accounts in
Author: |
Darinder Shokar |
Created at: |
Mar 2023 |
Updated at: |
May 2024 |
By
Darinder
Shokar
Originally posted on https://medium.com/@darinder.shokar
Introduction
In this blog I’ll present a scripted approach for Service Account creation and use in ForgeRock Identity Cloud. However, before I do let’s discuss a little context for the why and how:
Many customers want to manage the configuration they apply to ForgeRock Identity Cloud as code from a central repository and push via a CI/CD pipeline. This approach has multiple benefits:
-
Single repository to manage — Configuration is typically stored in a single central repository which eases management for config additions, modifies, deletes and long term maintenance.
-
Standardised configuration — As all config is central, it is far easier to define and enforce standards for code, testing, etc.
-
Traceability — Customers need to adapt to an ever changing landscape often, which means they need the agility to apply new or change existing configuration often. This introduces risk. A single repo for config, which is standardised and tested enables rapid for issue identification, isolation and remediation, thus greatly reducing both the likelihood and impact of config change going wrong.
The enabler for this approach and methodology in ForgeRock Identity Cloud is Service Accounts.

This a new feature to pragmatically request scoped access tokens to call
API endpoints without relying on a human user identity in the system.
Token generation is based on standards; in this case the OAuth2
JWT_Bearer standard and scopes ensure only the necessary permissions
are assigned to each access token.
To get a more detailed background of Service Accounts in ForgeRock Identity Cloud, check out this link.
Scripted Approach
Now we have an understanding of Service Accounts lets dive into how to create a service account, use it to generate a tightly scoped access token and then use this access token to call ForgeRock Identity Cloud APIs — all via a single script!
The script is located on Github here.
In order to execute and for segregation of duties reasons the script must be executed with a Tenant Admin user’s access token. For example:
./service_accounts.sh eyJ0eXAiOiJKV...To acquire this Tenant Admin access token, the easiest way is to inspect the browser Developer Tools on login to ForgeRock Identity Cloud as a Tenant Admin and look for the Authorization: Bearer header in the Network Request calls and copy the JWT token to somewhere safe.
The output from executing the script with a valid tenant admin access token will look like this:
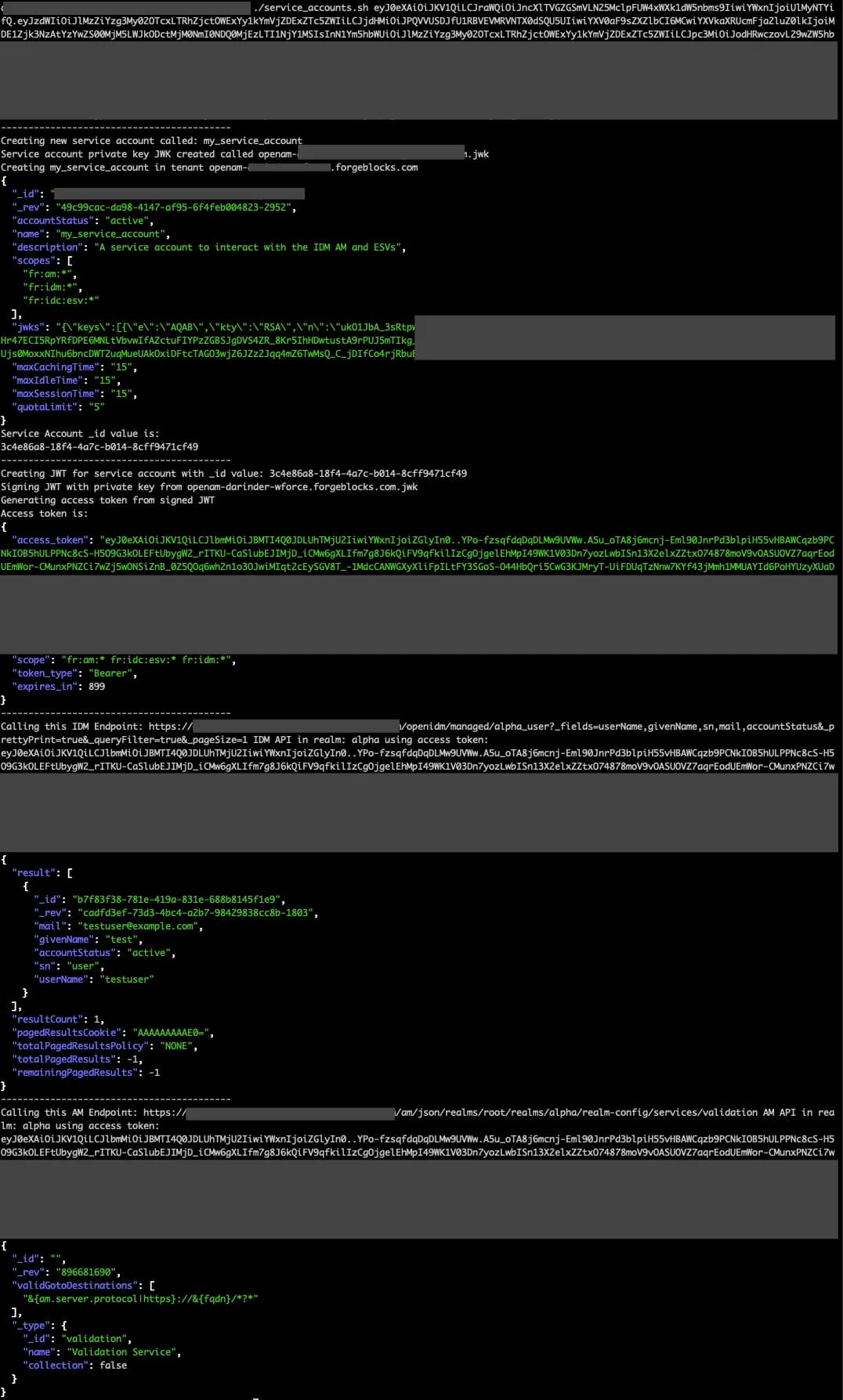
Script Breakdown
Here’s a breakdown of the various functions:
Checks — The script requires openSSL, jq and jose installed on
the target system. The opensslCheck, jqCheck and joseCheck
functions verify presence and exit if not found. Ensure they tools are
deployed before executing the script.
createServiceAccount — This function creates a Service Account in a
ForgeRock Identity Cloud tenant. It creates an RSA256 Private Key JWK
using the jose tool on disk, provisions a service account in ForgeRock
Identity Cloud called my_service_account with
fr:am:* fr:idm:* fr:idc:esv:* scopes defined using this JWK and on
success stores the immutable _id value of the account to a file on
disk for later use.
Note: Be sure to re-use a Service Account rather than creating a new
one on every execution of the script by commenting out the
createServiceAccount function on line 144 after the first run.
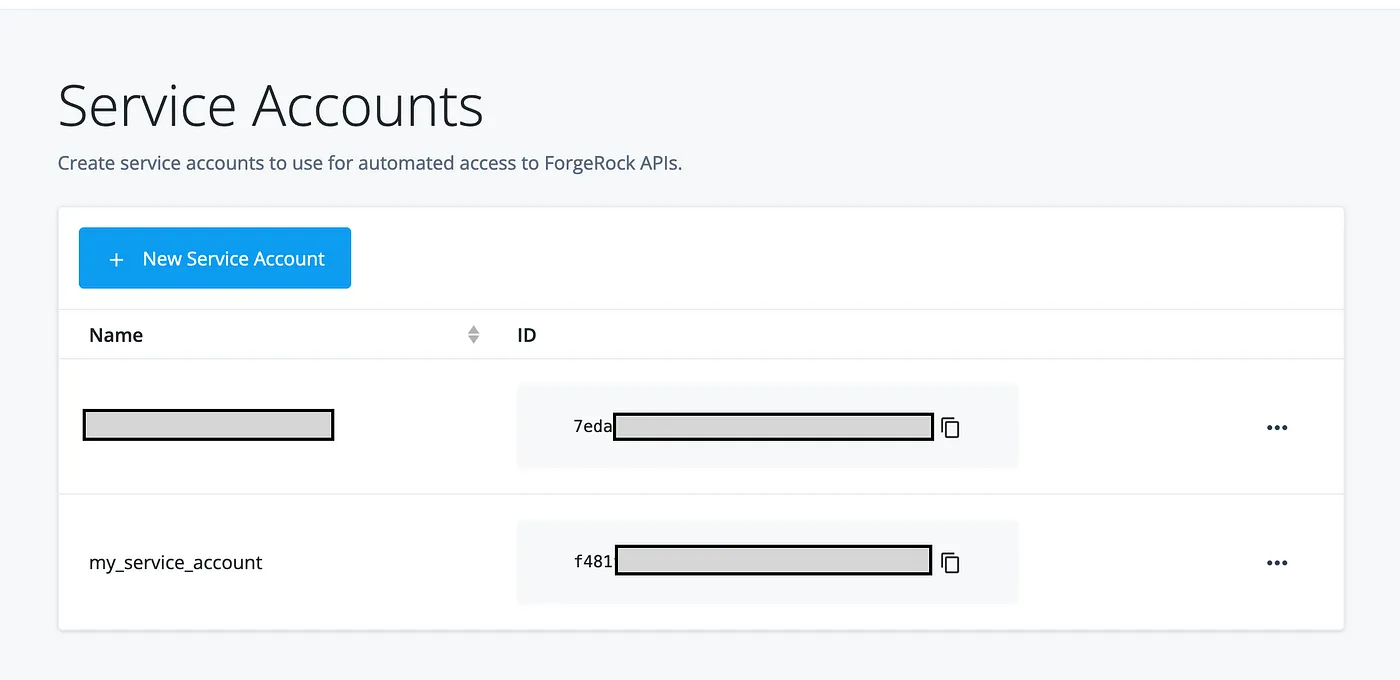
After execution, from the ForgeRock Platform Admin UI > Top right drop down > Tenant settings > Service Accounts, you’ll see our new Service Account listed:
getAccessToken — This function checks the Service Account _id
(account_id.txt) and private key JWK (<tenant>.jwk) files are
present on disk before acquiring an access token scoped to
fr:am:* fr:idm:* fr:idc:esv:* by executing the OAuth2 JWT_Bearer flow.
callIDM — This function calls an IDM endpoint to retrieve a single user via the Service Account access token to demonstrate usage.
callAM — This function calls an AM endpoint to retrieve the configuration for the AM validation service to demonstrate usage.
Conclusion
So there you have it, a scripted approach to create and use Service Accounts in ForgeRock Identity Cloud to power managing configuration as code for CI/CD pipelines.
The great thing about ForgeRock Identity Cloud is it is constantly evolving to add cool new features and capabilities with zero downtime or engineering effort from the customer. They log out on Monday and login on Monday and suddently there’s this cool new thing to play with :)
Look out for more blogs on the latest and greatest coming soon and thanks for reading!
+
A Scripted Approach for Creating and Using Service Accounts in ForgeRock…
A scripted approach for creating and using the new Service Accounts feature in ForgeRock Identity Cloud
Reading time: 4 min read
![]() How
to Count the Total Number of Remote Users in ForgeRock Identity Cloud
[.badge-category__name#Setup#]
How
to Count the Total Number of Remote Users in ForgeRock Identity Cloud
[.badge-category__name#Setup#]
By Darinder Shokar Originally posted on https://medium.com/@darinder.shokar Introduction ForgeRock Identity Cloud allows you to connect your tenant to an external data source such as an LDAP server or database. From time to time there is a need to count the total number of users (or objects) in such a datastore. [Total User Count] Total User Count This blog presents a programmatic way to execute a count quickly and easily in Identity Cloud using the …/system endpoint. As a pre-requisi…
Problem statement Most database technologies (Cloud DB as a Service offerings, traditional DBs, LDAP services, etc.) typically run in a single primary mode, with multiple secondary nodes to ensure high availability. The main rationale is it’s the only surefire way to ensure data consistency, and integrity is maintained. If an active topology was enabled, replication delay (the amount of time it takes for a data WRITE operation on one node to propagate to a peer) may cause the following to occu…
![]() Use
case: Use email address as the username in ForgeRock Identity Cloud
[.badge-category__name#Setup#]
Use
case: Use email address as the username in ForgeRock Identity Cloud
[.badge-category__name#Setup#]
Use case overview Many organizations, particularly those in the Consumer Identity & Access Management (CIAM) space, want to enable a slick low friction experience for their customers. One easy way to achieve this is by using the email address as the username, rather than customers having to remember words or a set of characters. Steps to achieve this use case A key feature and differentiator of ForgeRock Identity Cloud is its flexibility. You can take advantage of this flexibility to configur…
![]() Immutable
Deployment Pattern for AM Configuration Without File- Based
Configuration
[.badge-category__name#Architecture#]
Immutable
Deployment Pattern for AM Configuration Without File- Based
Configuration
[.badge-category__name#Architecture#]
[image] Introduction The standard production grade deployment pattern for ForgeRock Access Management (AM) is to use replicated sets of configuration directory server instances to store all of AM’s configurations. The deployment pattern has worked well in the past, but is less suited to the immutable, DevOps-enabled environments of today. This article presents an alternative view of how an immutable deployment pattern could be applied to AM in lieu of the upcoming, full file-based configura…
![]() Immutable
Deployment Pattern for ForgeRock Access Management (AM) Configuration
without File Based Configuration (FBC)
[.badge-category__name#Architecture#]
Immutable
Deployment Pattern for ForgeRock Access Management (AM) Configuration
without File Based Configuration (FBC)
[.badge-category__name#Architecture#]
Introduction The standard Production Grade deployment pattern for ForgeRock AM is to use replicated sets of Configuration Directory Server instances to store all of AM’s configuration. The deployment pattern has worked well in the past, but is less suited to the immutable, DevOps enabled environments of today. This blog presents an alternative view of how an immutable deployment pattern could be applied to AM in lieu of the upcoming full File Based Configuration (FBC) for AM in version 7.0 of…
![]() IDM
Deployment Patterns: Centralized Repo- Based vs. Immutable File-Based
[.badge-category__name#Architecture#]
IDM
Deployment Patterns: Centralized Repo- Based vs. Immutable File-Based
[.badge-category__name#Architecture#]
Introduction I recently blogged about how customers can architect ForgeRock Access Management to support an immutable, DevOps style deployment pattern — see link. In this post, we’ll take a look at how to do this for ForgeRock Identity Management (IDM). IDM is a modern OSGi-based application, with its configuration stored as a set of JSON files. This lends itself well to either a centralized repository- (repo) based deployment pattern, or a file-based immutable pattern. This article explores …
![]() A
Script for Executing the OAuth 2.0 Authorization Code Flow with PKCE in
AM [.badge-category__name#Setup#]
A
Script for Executing the OAuth 2.0 Authorization Code Flow with PKCE in
AM [.badge-category__name#Setup#]
Introduction I often meet customers who want to quickly understand how the OAuth2 Authorization Code grant type works, how Proof Key for Code Exchange (PKCE) works, and how they can execute the flows programatically to understand how it all hangs together. This blog provides a sample script to execute the OAuth2 Authorization Code grant flow, along with support for PKCE using cURL. What is the OAuth2 Authorization Code Grant Flow? The Authorization Code grant is a two-step interactive proces…
Introduction ForgeRock Identity Cloud is revolutionizing the way businesses, consumers, and customers execute on their IAM strategy. Our Identity Cloud customers repeat three common feedback themes over and over again: Quicker time to value: Customers no longer have to worry about the build, run, operate and feed process of standing up an IAM system—ForgeRock Identity Cloud is managed by the people who build the underlying software; us (ForgeRock). Introduction of cool new stuff quicker and …
![]() Integrating IG with Identity
Cloud
[.badge-category__name#Integrations#]
Integrating IG with Identity
Cloud
[.badge-category__name#Integrations#]
Introduction It’s an exciting time here at ForgeRock. The ForgeRock Identity Cloud helps customers rapidly embrace next generation IAM, and quickly realize a return on their investment. For more on what this service offers, check out the following links: ForgeRock Identity Cloud overview here. ForgeRock Identity Cloud documentation here. In this exciting world, helping customers quickly and easily integrate with the ForgeRock Identity Cloud platform is critical. In this article, we’ll show yo…
![]() Locking
Out a User and Deleting All of Their Active Tokens in AM
[.badge-category__name#Maintenance#]
Locking
Out a User and Deleting All of Their Active Tokens in AM
[.badge-category__name#Maintenance#]
Introduction Customers often ask, “We have a business security requirement where we want to not only lock a given user out of the system, but also find and delete all SSO tokens they have created using the AM API. How do we do that?” This article shows you how to do this using the delete_tokens.sh script ;) In order to achieve this, we’ll be making using of the following AM endpoints: …/authenticate: Endpoint for authenticating users. …/users: Endpoint for getting and setting user profile a…
