An All Active Persistent Data Layer? No Way! Yes Way!
Author: |
Darinder Shokar |
Created at: |
Sep 2019 |
Updated at: |
May 2024 |
Problem statement
Most database technologies (Cloud DB as a Service offerings, traditional DBs, LDAP services, etc.) typically run in a single primary mode, with multiple secondary nodes to ensure high availability. The main rationale is it’s the only surefire way to ensure data consistency, and integrity is maintained.
If an active topology was enabled, replication delay (the amount of time it takes for a data WRITE operation on one node to propagate to a peer) may cause the following to occur:
-
The client executes a WRITE operation on node 1.
-
The client then executes a READ operation soon after the WRITE.
-
In an all active topology this READ operation may target node 2, but because the data has not yet been replicated (due to load, network latency, etc) you get a data miss and application level chaos ensues.
Another scenario is lock counters:
-
User A is an avid Manchester UTD football fan (alas more of a curse than a blessing nowadays!) and is keen to watch the game. In haste, they try to login but supply an incorrect password. The lock counter increments by +1 on User A’s profile on node 1. Counter moves from 0 to 1.
-
User A, desperate to catch the game then quickly tries to login again, but again supplies an incorrect password.
-
This time, if replication is not quick enough, node 2 may be targeted and thus the lock counter moves from 0 to 1 instead of from 1 to 2. Fail!!!
These scenarios and others like it mandate a single primary topology, which for high load environments, results in high cost, as the primary needs to be vertically scaled to handle all of the load (plus headroom) and wasted compute resource as the secondaries (same spec as the primary) are sat idle costing $$$ for no gain.
Tada — Roll up Affinity Based Load Balancing
ForgeRock Directory Services (DS) is the high performance, high scale, LDAP-based persistent layer product within the ForgeRock Identity Platform. Any DS instance can take both WRITE and READ operations at scale; for many customers enabling an all active infrastructure without Affinity Based Load Balancing is viable.
However, for high scale customers and/or those who need to guarantee absolute consistency of data, then Affinity Based Load Balancing, a technology unique to the ForgeRock Identity Platform is the key to enabling an all active persistence layer. Nice!
Affinity what now?
It is a load balancing algorithm built into the DS SDK which is part of both the ForgeRock Directory Proxy product and the ForgeRock Access Management (AM) product.
It works like this:
For each and every inbound LDAP request which contains a distinguished name (DN) like uid=Darinder,ou=People,o=ForgeRock, the SDK takes a hash and allocates the result to a specific DS instance. In the case of AM, all servers in the pool compute the same hash, and thus send all READ/MODIFY/DELETE requests for uid=Darinder to say DS Node 1 (origin node).
A request with a different DN (e.g. uid=Ronaldo,ou=People,o=ForgeRock) is again hashed but may be sent to DS Node 2; all READ/MODIFY/DELETE operations for uid=Ronaldo target this specific origin node and so on. This means all READ/MODIFY/DELETE operations for a specific DN always target the same DS instance, thus eliminating issues caused by replication delay and solving the scenarios (and others) described in the Problem statement above. Sweet!
The following topology depicts this architecture:
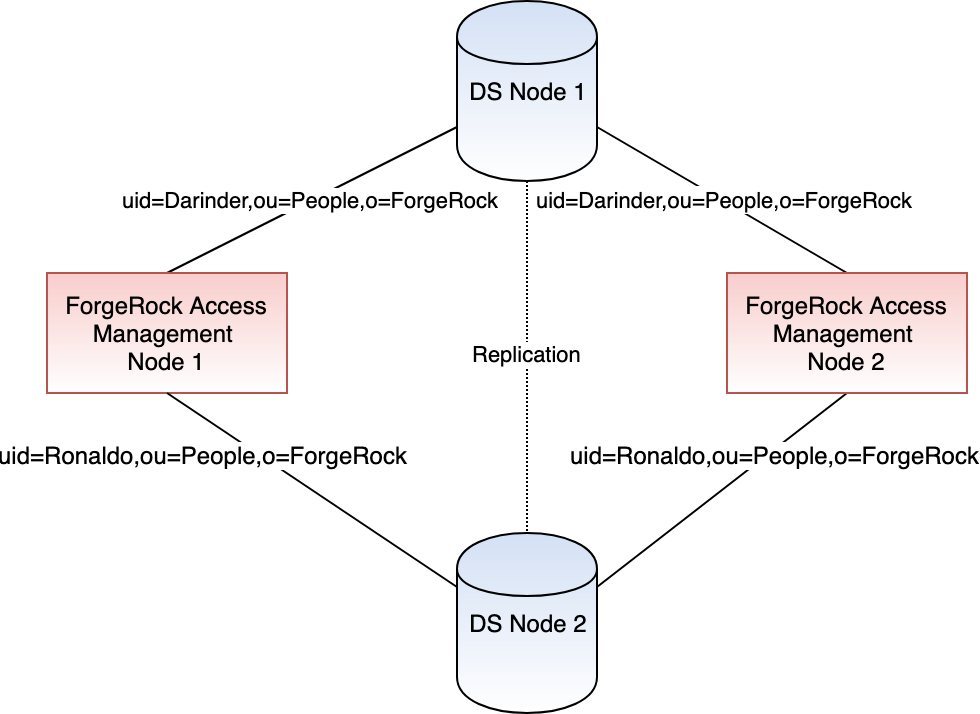
All requests from AM1 and AM2 for uid=Darinder target DS Node 1. All requests from AM1 and AM2 for uid=Ronaldo target DS Node 2.
What else does this trick DS SDK do then?
Well… The SDK also makes sure ADD requests are spread evenly across all DS nodes in the pool to not overloaded one DS node while the others remain idle.
Also for a bit of icing on top, the SDK is instance aware if the origin DS node becomes unavailable (in our example, say DS Node 1 for uid=Darinder), the SDK detects this and re-routes all requests for uid=Darinder to another DS node in the pool, and then (here’s the cherry) ensures all further requests remains sticky to this new DS node (it becomes the new origin node). Assuming data has been replicated in time; there will be no functional impact.
Oh, and when the original DS node comes back online, all requests fail back for any DNs where it was the origin server (so, in our case, uid=Darinder would flip back to DS Node 1). Booom!
Which components of the ForgeRock Platform support Affinity Based Load Balancing?
-
Directory Proxy
-
ForgeRock AM’s DS Core Token Service (CTS)
-
ForgeRock AM’s DS User / Identity Store
-
ForgeRock AM’s App and Policy Stores
Note: the AM Configuration Store does not support affinity but this is intentional as AM configuration will soon move to file-based configuration (FBC) and in the interim customers can look to deploy like this.
What are the advantages of Affinity?
-
As the title says, Affinity Based Load Balancing enables an active persistent storage layer
-
Instead of having a single massively vertically scaled primary DS instance, DS can be horizontally scaled so all nodes are primary to increase throughput and maximise compute resource.
-
As the topology is all active, smaller (read: cheaper) instances can be used; thus, significantly reducing costs, especially in a Cloud environment.
-
Eliminates functional, data integrity, and data consistency issues causes by replication delay.
More Innnnput!
To learn more about how to configure ForgeRock AM for Affinity Based Load Balancing check out this.
Other Articles by This Author
![]() Immutable
Deployment Pattern for AM Configuration Without File- Based
Configuration
[.badge-category__name#Architecture#]
Immutable
Deployment Pattern for AM Configuration Without File- Based
Configuration
[.badge-category__name#Architecture#]
[image] Introduction The standard production grade deployment pattern for ForgeRock Access Management (AM) is to use replicated sets of configuration directory server instances to store all of AM’s configurations. The deployment pattern has worked well in the past, but is less suited to the immutable, DevOps-enabled environments of today. This article presents an alternative view of how an immutable deployment pattern could be applied to AM in lieu of the upcoming, full file-based configura…
![]() Integrating IG with Identity
Cloud
[.badge-category__name#Integrations#]
Integrating IG with Identity
Cloud
[.badge-category__name#Integrations#]
Introduction It’s an exciting time here at ForgeRock. The ForgeRock Identity Cloud helps customers rapidly embrace next generation IAM, and quickly realize a return on their investment. For more on what this service offers, check out the following links: ForgeRock Identity Cloud overview here. ForgeRock Identity Cloud documentation here. In this exciting world, helping customers quickly and easily integrate with the ForgeRock Identity Cloud platform is critical. In this article, we’ll show yo…
![]() Locking
Out a User and Deleting All of Their Active Tokens in AM
[.badge-category__name#Maintenance#]
Locking
Out a User and Deleting All of Their Active Tokens in AM
[.badge-category__name#Maintenance#]
Introduction Customers often ask, “We have a business security requirement where we want to not only lock a given user out of the system, but also find and delete all SSO tokens they have created using the AM API. How do we do that?” This article shows you how to do this using the delete_tokens.sh script ;) In order to achieve this, we’ll be making using of the following AM endpoints: …/authenticate: Endpoint for authenticating users. …/users: Endpoint for getting and setting user profile a…
![]() A
Script for Executing the OAuth 2.0 Authorization Code Flow with PKCE in
AM [.badge-category__name#Setup#]
A
Script for Executing the OAuth 2.0 Authorization Code Flow with PKCE in
AM [.badge-category__name#Setup#]
Introduction I often meet customers who want to quickly understand how the OAuth2 Authorization Code grant type works, how Proof Key for Code Exchange (PKCE) works, and how they can execute the flows programatically to understand how it all hangs together. This blog provides a sample script to execute the OAuth2 Authorization Code grant flow, along with support for PKCE using cURL. What is the OAuth2 Authorization Code Grant Flow? The Authorization Code grant is a two-step interactive proces…
![]() Use
case: Use email address as the username in ForgeRock Identity Cloud
[.badge-category__name#Setup#]
Use
case: Use email address as the username in ForgeRock Identity Cloud
[.badge-category__name#Setup#]
Use case overview Many organizations, particularly those in the Consumer Identity & Access Management (CIAM) space, want to enable a slick low friction experience for their customers. One easy way to achieve this is by using the email address as the username, rather than customers having to remember words or a set of characters. Steps to achieve this use case A key feature and differentiator of ForgeRock Identity Cloud is its flexibility. You can take advantage of this flexibility to configur…
Introduction ForgeRock Identity Cloud is revolutionizing the way businesses, consumers, and customers execute on their IAM strategy. Our Identity Cloud customers repeat three common feedback themes over and over again: Quicker time to value: Customers no longer have to worry about the build, run, operate and feed process of standing up an IAM system—ForgeRock Identity Cloud is managed by the people who build the underlying software; us (ForgeRock). Introduction of cool new stuff quicker and …